Реализация.
Сущность и основные виды шифрования
Advanced Encryption Standard (AES), также известный как Rijndael (произносится (Рэндал)) — симметричный алгоритм блочного шифрования (размер блока 128 бит, ключ 128/192/256 бит), принятый в качестве стандарта шифрования правительством США по результатам конкурса AES. Этот алгоритм хорошо проанализирован и сейчас широко используется, как это было с его предшественником DES. Национальный институт… Читать ещё >
Реализация. Сущность и основные виды шифрования (реферат, курсовая, диплом, контрольная)
Для реализации были выбраны два алгоритма :
Симметричный — AES.
Ассиметричный — RSA.
Advanced Encryption Standard (AES), также известный как Rijndael (произносится [r?inda?l] (Рэндал[1])) — симметричный алгоритм блочного шифрования (размер блока 128 бит, ключ 128/192/256 бит), принятый в качестве стандарта шифрования правительством США по результатам конкурса AES. Этот алгоритм хорошо проанализирован и сейчас широко используется, как это было с его предшественником DES. Национальный институт стандартов и технологий США (англ. National Institute of Standards and Technology, NIST) опубликовал спецификацию AES 26 ноября 2001 года после пятилетнего периода, в ходе которого были созданы и оценены 15 кандидатур. 26 мая 2002 года AES был объявлен стандартом шифрования. По состоянию на 2009 год AES является одним из самых распространённых алгоритмов симметричного шифрования.
Aes.py.
Sbox = (.
- 0x63, 0x7C, 0×77, 0x7B, 0xF2, 0x6B, 0x6 °F, 0xC5, 0×30, 0×01, 0×67, 0x2B, 0xFE, 0xD7, 0xAB, 0×76,
- 0xCA, 0×82, 0xC9, 0x7D, 0xFA, 0×59, 0×47, 0xF0, 0xAD, 0xD4, 0xA2, 0xAF, 0x9C, 0xA4, 0×72, 0xC0,
- 0xB7, 0xFD, 0×93, 0×26, 0×36, 0x3 °F, 0xF7, 0xCC, 0×34, 0xA5, 0xE5, 0xF1, 0×71, 0xD8, 0×31, 0×15,
- 0x04, 0xC7, 0×23, 0xC3, 0×18, 0×96, 0×05, 0x9A, 0×07, 0×12, 0×80, 0xE2, 0xEB, 0×27, 0xB2, 0×75,
- 0x09, 0×83, 0x2C, 0x1A, 0x1B, 0x6E, 0x5A, 0xA0, 0×52, 0x3B, 0xD6, 0xB3, 0×29, 0xE3, 0x2 °F, 0×84,
- 0x53, 0xD1, 0×00, 0xED, 0×20, 0xFC, 0xB1, 0x5B, 0x6A, 0xCB, 0xBE, 0×39, 0x4A, 0x4C, 0×58, 0xCF,
- 0xD0, 0xEF, 0xAA, 0xFB, 0×43, 0x4D, 0×33, 0×85, 0×45, 0xF9, 0×02, 0x7 °F, 0×50, 0x3C, 0x9 °F, 0xA8,
- 0x51, 0xA3, 0×40, 0x8 °F, 0×92, 0x9D, 0×38, 0xF5, 0xBC, 0xB6, 0xDA, 0×21, 0×10, 0xFF, 0xF3, 0xD2,
- 0xCD, 0x0C, 0×13, 0xEC, 0x5 °F, 0×97, 0×44, 0×17, 0xC4, 0xA7, 0x7E, 0x3D, 0×64, 0x5D, 0×19, 0×73,
- 0x60, 0×81, 0x4 °F, 0xDC, 0×22, 0x2A, 0×90, 0×88, 0×46, 0xEE, 0xB8, 0×14, 0xDE, 0x5E, 0x0B, 0xDB,
- 0xE0, 0×32, 0x3A, 0x0A, 0×49, 0×06, 0×24, 0x5C, 0xC2, 0xD3, 0xAC, 0×62, 0×91, 0×95, 0xE4, 0×79,
- 0xE7, 0xC8, 0×37, 0x6D, 0x8D, 0xD5, 0x4E, 0xA9, 0x6C, 0×56, 0xF4, 0xEA, 0×65, 0x7A, 0xAE, 0×08,
- 0xBA, 0×78, 0×25, 0x2E, 0x1C, 0xA6, 0xB4, 0xC6, 0xE8, 0xDD, 0×74, 0x1 °F, 0x4B, 0xBD, 0x8B, 0x8A,
- 0x70, 0x3E, 0xB5, 0×66, 0×48, 0×03, 0xF6, 0x0E, 0×61, 0×35, 0×57, 0xB9, 0×86, 0xC1, 0x1D, 0x9E,
- 0xE1, 0xF8, 0×98, 0×11, 0×69, 0xD9, 0x8E, 0×94, 0x9B, 0x1E, 0×87, 0xE9, 0xCE, 0×55, 0×28, 0xDF,
- 0x8C, 0xA1, 0×89, 0x0D, 0xBF, 0xE6, 0×42, 0×68, 0×41, 0×99, 0x2D, 0x0 °F, 0xB0, 0×54, 0xBB, 0×16,
).
InvSbox = (.
- 0x52, 0×09, 0x6A, 0xD5, 0×30, 0×36, 0xA5, 0×38, 0xBF, 0×40, 0xA3, 0x9E, 0×81, 0xF3, 0xD7, 0xFB,
- 0x7C, 0xE3, 0×39, 0×82, 0x9B, 0x2 °F, 0xFF, 0×87, 0×34, 0x8E, 0×43, 0×44, 0xC4, 0xDE, 0xE9, 0xCB,
- 0x54, 0x7B, 0×94, 0×32, 0xA6, 0xC2, 0×23, 0x3D, 0xEE, 0x4C, 0×95, 0x0B, 0×42, 0xFA, 0xC3, 0x4E,
- 0x08, 0x2E, 0xA1, 0×66, 0×28, 0xD9, 0×24, 0xB2, 0×76, 0x5B, 0xA2, 0×49, 0x6D, 0x8B, 0xD1, 0×25,
- 0x72, 0xF8, 0xF6, 0×64, 0×86, 0×68, 0×98, 0×16, 0xD4, 0xA4, 0x5C, 0xCC, 0x5D, 0×65, 0xB6, 0×92,
- 0x6C, 0×70, 0×48, 0×50, 0xFD, 0xED, 0xB9, 0xDA, 0x5E, 0×15, 0×46, 0×57, 0xA7, 0x8D, 0x9D, 0×84,
- 0x90, 0xD8, 0xAB, 0×00, 0x8C, 0xBC, 0xD3, 0x0A, 0xF7, 0xE4, 0×58, 0×05, 0xB8, 0xB3, 0×45, 0×06,
- 0xD0, 0x2C, 0x1E, 0x8 °F, 0xCA, 0x3 °F, 0x0 °F, 0×02, 0xC1, 0xAF, 0xBD, 0×03, 0×01, 0×13, 0x8A, 0x6B,
- 0x3A, 0×91, 0×11, 0×41, 0x4 °F, 0×67, 0xDC, 0xEA, 0×97, 0xF2, 0xCF, 0xCE, 0xF0, 0xB4, 0xE6, 0×73,
- 0x96, 0xAC, 0×74, 0×22, 0xE7, 0xAD, 0×35, 0×85, 0xE2, 0xF9, 0×37, 0xE8, 0x1C, 0×75, 0xDF, 0x6E,
- 0x47, 0xF1, 0x1A, 0×71, 0x1D, 0×29, 0xC5, 0×89, 0x6 °F, 0xB7, 0×62, 0x0E, 0xAA, 0×18, 0xBE, 0x1B,
- 0xFC, 0×56, 0x3E, 0x4B, 0xC6, 0xD2, 0×79, 0×20, 0x9A, 0xDB, 0xC0, 0xFE, 0×78, 0xCD, 0x5A, 0xF4,
- 0x1 °F, 0xDD, 0xA8, 0×33, 0×88, 0×07, 0xC7, 0×31, 0xB1, 0×12, 0×10, 0×59, 0×27, 0×80, 0xEC, 0x5 °F,
- 0x60, 0×51, 0x7 °F, 0xA9, 0×19, 0xB5, 0x4A, 0x0D, 0x2D, 0xE5, 0x7A, 0x9 °F, 0×93, 0xC9, 0x9C, 0xEF,
- 0xA0, 0xE0, 0x3B, 0x4D, 0xAE, 0x2A, 0xF5, 0xB0, 0xC8, 0xEB, 0xBB, 0x3C, 0×83, 0×53, 0×99, 0×61,
- 0x17, 0x2B, 0×04, 0x7E, 0xBA, 0×77, 0xD6, 0×26, 0xE1, 0×69, 0×14, 0×63, 0×55, 0×21, 0x0C, 0x7D,
).
xtime = lambda a: (((a << 1) ^ 0x1B) & 0xFF) if (a & 0×80) else (a << 1).
Rcon = (.
- 0x00, 0×01, 0×02, 0×04, 0×08, 0×10, 0×20, 0×40,
- 0x80, 0x1B, 0×36, 0x6C, 0xD8, 0xAB, 0x4D, 0x9A,
- 0x2 °F, 0x5E, 0xBC, 0×63, 0xC6, 0×97, 0×35, 0x6A,
- 0xD4, 0xB3, 0x7D, 0xFA, 0xEF, 0xC5, 0×91, 0×39,
).
def text2matrix (text):
matrix = [].
for i in range (16):
byte = (text >> (8 * (15 — i))) & 0xFF.
if i % 4 == 0:
matrix.append ([byte]).
else:
matrix[i / 4]. append (byte).
return matrix.
def matrix2text (matrix):
text = 0.
for i in range (4):
for j in range (4):
text |= (matrix[i][j] << (120 — 8 * (4 * i + j))).
return text.
class AES:
def __init__(self, master_key):
self.change_key (master_key).
def change_key (self, master_key):
self.round_keys = text2matrix (master_key).
# print self. round_keys.
for i in range (4, 4 * 11):
self.round_keys.append ([]).
if i % 4 == 0:
byte = self. round_keys[i — 4][0].
^ Sbox[self.round_keys[i — 1][1]].
^ Rcon[i / 4].
self.round_keys[i]. append (byte).
for j in range (1, 4):
byte = self. round_keys[i — 4][j].
^ Sbox[self.round_keys[i — 1][(j + 1) % 4]].
self.round_keys[i]. append (byte).
else:
for j in range (4):
byte = self. round_keys[i — 4][j].
^ self. round_keys[i — 1][j].
self.round_keys[i]. append (byte).
# print self. round_keys.
def encrypt (self, plaintext):
self.plain_state = text2matrix (plaintext).
self.__add_round_key (self.plain_state, self. round_keys[:4]).
for i in range (1, 10):
self.__round_encrypt (self.plain_state, self. round_keys[4 * i: 4 * (i + 1)]).
self.__sub_bytes (self.plain_state).
self.__shift_rows (self.plain_state).
self.__add_round_key (self.plain_state, self. round_keys[40:]).
return matrix2text (self.plain_state).
def decrypt (self, ciphertext):
self.cipher_state = text2matrix (ciphertext).
self.__add_round_key (self.cipher_state, self. round_keys[40:]).
self.__inv_shift_rows (self.cipher_state).
self.__inv_sub_bytes (self.cipher_state).
for i in range (9, 0, -1):
self.__round_decrypt (self.cipher_state, self. round_keys[4 * i: 4 * (i + 1)]).
self.__add_round_key (self.cipher_state, self. round_keys[:4]).
return matrix2text (self.cipher_state).
def __add_round_key (self, s, k):
for i in range (4):
for j in range (4):
s[i][j] ^= k[i][j].
def __round_encrypt (self, state_matrix, key_matrix):
self.__sub_bytes (state_matrix).
self.__shift_rows (state_matrix).
self.__mix_columns (state_matrix).
self.__add_round_key (state_matrix, key_matrix).
def __round_decrypt (self, state_matrix, key_matrix):
self.__add_round_key (state_matrix, key_matrix).
self.__inv_mix_columns (state_matrix).
self.__inv_shift_rows (state_matrix).
self.__inv_sub_bytes (state_matrix).
def __sub_bytes (self, s):
for i in range (4):
for j in range (4):
s[i][j] = Sbox[s[i][j]].
def __inv_sub_bytes (self, s):
for i in range (4):
for j in range (4):
s[i][j] = InvSbox[s[i][j]].
def __shift_rows (self, s):
s[0][1], s[1][1], s[2][1], s[3][1] = s[1][1], s[2][1], s[3][1], s[0][1].
s[0][2], s[1][2], s[2][2], s[3][2] = s[2][2], s[3][2], s[0][2], s[1][2].
s[0][3], s[1][3], s[2][3], s[3][3] = s[3][3], s[0][3], s[1][3], s[2][3].
def __inv_shift_rows (self, s):
s[0][1], s[1][1], s[2][1], s[3][1] = s[3][1], s[0][1], s[1][1], s[2][1].
s[0][2], s[1][2], s[2][2], s[3][2] = s[2][2], s[3][2], s[0][2], s[1][2].
s[0][3], s[1][3], s[2][3], s[3][3] = s[1][3], s[2][3], s[3][3], s[0][3].
def __mix_single_column (self, a):
# please see Sec 4.1.2 in The Design of Rijndael.
t = a[0] ^ a[1] ^ a[2] ^ a[3].
u = a[0].
a[0] ^= t ^ xtime (a[0] ^ a[1]).
a[1] ^= t ^ xtime (a[1] ^ a[2]).
a[2] ^= t ^ xtime (a[2] ^ a[3]).
a[3] ^= t ^ xtime (a[3] ^ u).
def __mix_columns (self, s):
for i in range (4):
self.__mix_single_column (s[i]).
def __inv_mix_columns (self, s):
# see Sec 4.1.3 in The Design of Rijndael.
for i in range (4):
u = xtime (xtime (s[i][0] ^ s[i][2])).
v = xtime (xtime (s[i][1] ^ s[i][3])).
s[i][0] ^= u.
s[i][1] ^= v.
s[i][2] ^= u.
s[i][3] ^= v.
self.__mix_columns (s).
test.py.
import unittest.
rom aes import AES.
class AES_TEST (unittest.TestCase):
def setUp (self):
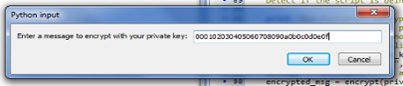
master_key = 0×10 203 040 506 070 8080a0b0c0d0e0f.
self.AES = AES (master_key).
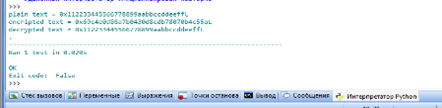
def test_encryption_decription (self):
laintext = 0×11 223 344 556 677 8889aabbccddeeff.
print «plain text =», hex (plaintext).
encrypted = self.AES.encrypt (plaintext).
print «encripted text =», hex (encrypted).
decrypted = self.AES.decrypt (encrypted).
print «decrypted text =», hex (decrypted).
if __name__ == '__main__':
unittest.main ().
RSA.py.
import random.
def gcd (a, b):
while b ≠ 0:
a, b = b, a % b.
return a.
def multiplicative_inverse (e, phi):
d = 0.
x1 = 0.
x2 = 1.
y1 = 1.
temp_phi = phi.
while e > 0:
temp1 = temp_phi/e.
temp2 = temp_phi — temp1 * e.
temp_phi = e.
e = temp2.
x = x2- temp1* x1.
y = d — temp1 * y1.
x2 = x1.
x1 = x.
d = y1.
y1 = y.
if temp_phi == 1:
return d + phi.
def is_prime (num):
if num == 2:
return True.
if num < 2 or num % 2 == 0:
return False.
for n in xrange (3, int (num**0.5)+2, 2):
if num % n == 0:
return False.
return True.
def generate_keypair (p, q):
if not (is_prime (p) and is_prime (q)):
raise ValueError ('Both numbers must be prime.').
elif p == q:
raise ValueError ('p and q cannot be equal').
#n = pq.
n = p * q.
phi = (p-1) * (q-1).
# Vybrat' tseloye chislo takoye, chto ye i fi (p) vzaimno prosty.
e = random. randrange (1, phi).
#ispol Algoritm Yevklida proverit', chto ye i fi (N) vzaimno prosty.
g = gcd (e, phi).
while g ≠ 1:
e = random. randrange (1, phi).
g = gcd (e, phi).
#use Rasshirennogo algoritma Yevklida dlya generirovaniya sekretnyy klyuch.
d = multiplicative_inverse (e, phi).
#Return zakrytogo i chastnogo pary klyuchey.
#Public Klyuch (ye, p) i zakrytyy klyuch (D, N).
return ((e, n), (d, n)).
def encrypt (pk, plaintext):
key, n = pk.
#Convert Kazhdoy bukvy v nezashifrovannom vide na nomera, osnovannogo na kharaktere, ispol’zuya ^ b?? mod m.
cipher = [(ord (char) ** key) % n for char in plaintext].
#Return massiv bytes.
return cipher.
def decrypt (pk, ciphertext):
#Unpack Klyuch v yeye komponentov.
key, n = pk.
#Generate Otkrytyy tekst na osnove zashifrovannogo.
#teksta i klyucha, ispol’zuya ^ b?? mod m.
plain = [chr ((char ** key) % n) for char in ciphertext].
#Return Massiv baytov v vide stroki.
return ''.join (plain).
if __name__ == '__main__':
'''.
Detect if the script is being run directly by the user.
'''.
print «RSA Encrypter/ Decrypter» .
p = int (raw_input («Enter a prime number (17, 19, 23, etc): «)).
q = int (raw_input («Enter another prime number (Not one you entered above): «)).
print «Generating your public/private keypairs now.. .» .
public, private = generate_keypair (p, q).
print «Your public key is «, public ,» and your private key is «, private.
message = raw_input («Enter a message to encrypt with your private key: «).
encrypted_msg = encrypt (private, message).
print «Your encrypted message is: «.
print ''.join (map (lambda x: str (x), encrypted_msg)).
print «Decrypting message with public key „, public ,“.. .» .
print «Your message is:» .
print decrypt (public, encrypted_msg).